Generating Your Own Threat Intelligence Feeds in ThreatStream
Recently we launched a feature that allows you to create your own threat intelligence feeds in CSV, JSON and STIX format. They're super simple to setup...


Getting threat intelligence into your existing security products - SIEMs, endpoints, network tools -- can significantly enhance their effectiveness and longevity. Here at Anomali we understand the value of product integrations, so much so that my entire job is to manage the 30+ we currently offer.
Recently we launched a feature that allows you to create your own threat intelligence feeds in CSV, JSON and STIX format for consumption by other products. They're super simple to setup...
Step One: Create a Saved Search
Use ThreatStream's search functionality to define the type of indicators you want to include in your feed. I used the search:
(itype="mal_domain") and (status="active") and (confidence>=95)
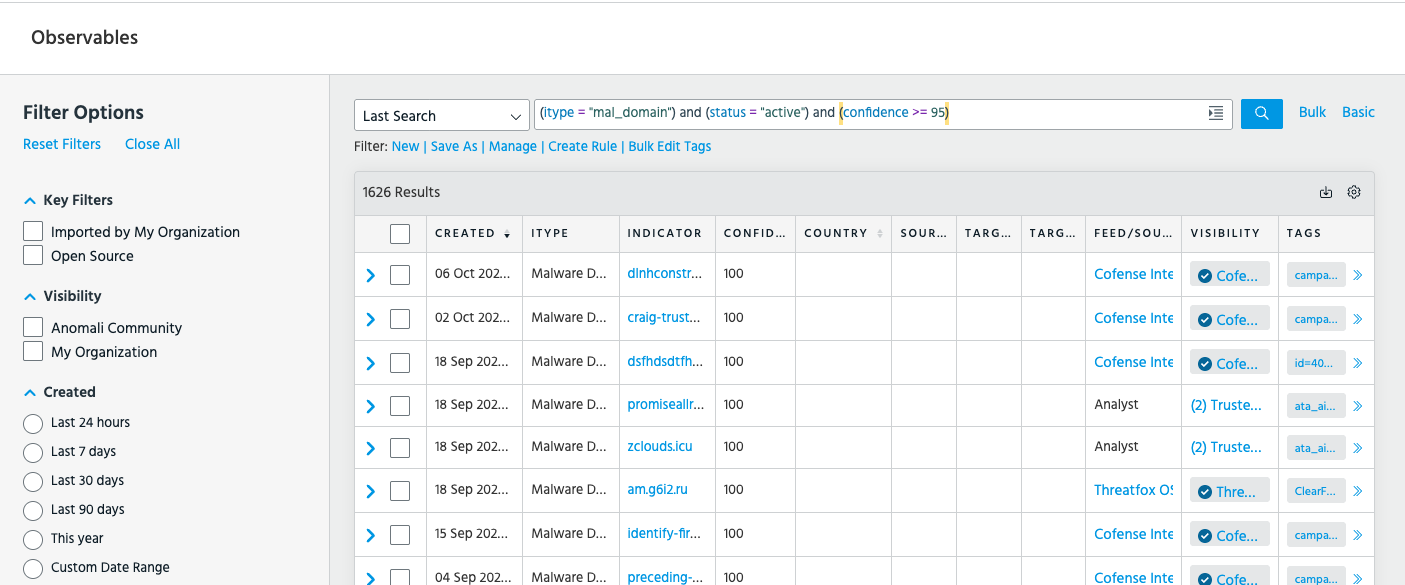
Translated into English; only include malware domain indicators type that are currently reported as active with a very high confidence score of 95 assigned by ThreatStream.
Once the constraints meet the requirements for your feed, select "save as" to convert it into a saved search you can use across ThreatStream.
Step Two: Create a Custom Integration
In ThreatStream navigate to: Settings > Integrations > New Integration
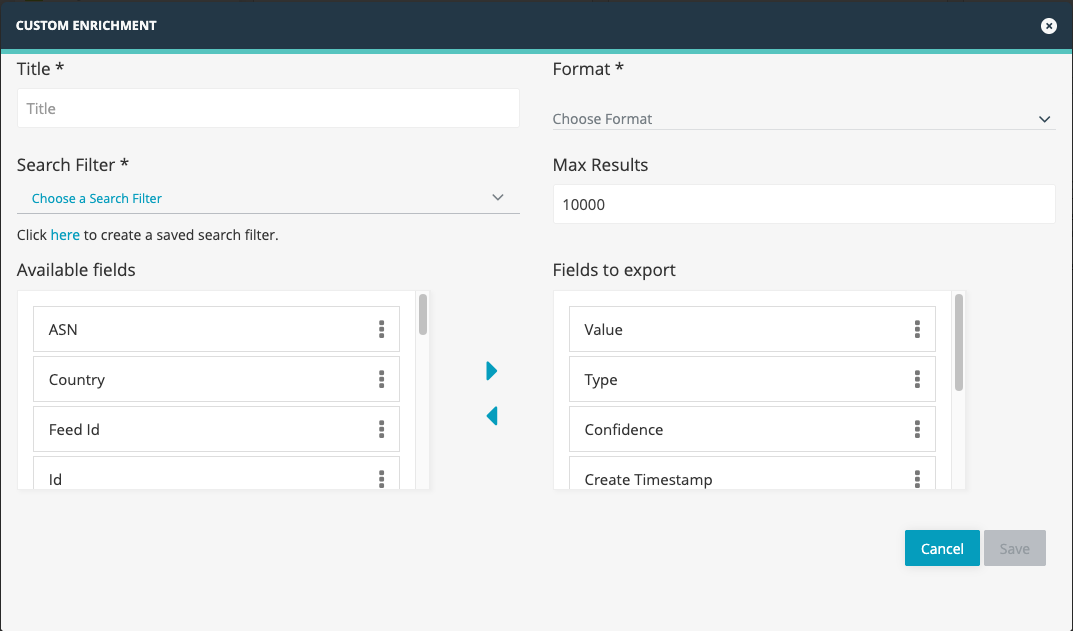
The pop-up modal will allow you to configure the settings for your feed including:
- The search filter (set in step one)
- The feed format (JSON, CSV or STIX)
- The fields to be included in the feed (35 available to select)
Once you hit save, ThreatStream will create a custom URL for your feed.
Step Three: Add Your Feed to Your Existing Products
You can now use the URL generated in step two as a feed source to any products that can ingest threat feeds in the configured format.
The feed is updated on a set schedule. If you're asked for a polling interval make sure to set it equal to this schedule so you're not making more requests than necessary.
My Product Does Not Support CSV, JSON or STIX Inputs
Trying to do integrate with a product that's a little more niche? Get in touch with our partnership team to explore a potential integration.
Discover More About Anomali
Get the latest news about cybersecurity, threat intelligence, and Anomali's Security and IT Operations platform.
Propel your mission with amplified visibility, analytics, and AI.
Learn how Anomali can help you cost-effectively improve your security posture.