The Anomali Blog

FEATURED BLOGS
Get the Anomali Newsletter
The latest Anomali updates and cybersecurity news, delivered straight to your inbox each month.
Why are we talking about Iran?
Over the last several months, Iran has been known to be supporting the conflicts between Israel and Hamas in Gaza and Israel and Hezbollah along the Lebanon border. And in truth, Iranian support for groups in opposition to Israel has been an enduring factor in the region for many years (e.g. proxies in Yemen, Syria and Iraq). News around the world in recent weeks has been dominated by the major uptick in the direct kinetic actions between Iran and Israel.
This series of kinetic actions, essentially in answer to one another, were backed by very strong rhetoric from both sides that led to very real fears of an escalation to a broader and more severe regional conflict that would rapidly draw in other major powers and allies.
For now, however, it appears that the risk of war with Iran has a ‘lid on it’ - it could not be said that it has been averted - everyone is watching the situation carefully, and it remains a tinderbox. International efforts continue to drive towards a sustained ceasefire in Gaza, de-escalation of that conflict and humanitarian aid.
Should we worry about an increased cyber threat from Iran?
It must also be remembered that in the modern era, conflict is asymmetric - made up of traditional military tactics and actions combined with cyber positioning and attacks. As we witness a de-escalation of the kinetic side of the conflict, we should expect to see continued and most likely increased cyber action.
How competent is Iran in cyberspace?
Iran is a highly competent and active cyber threat worldwide. Their combination of state-sponsored cyber operations, espionage activities, disruptive attacks, and geopolitical motivations make them a potent threat. They have spent years investing in their cyber capabilities by combining a resilient cyber infrastructure with highly trained and skilled personnel.
Iran’s investment in its cyber capability pre-dates the infamous Stuxnet incident of 2010 that directly attacked their nuclear programme, critically damaging the centrifuges at the Natanz uranium enrichment plant. But there is no doubt that the Stuxnet worm attack (speculatively attributed to the US and Israel) caused Iran to intensify its efforts to develop offensive cyber capabilities and resilience.
Iran has earned its place on the world stage as a cyber threat actor, spanning state-sponsored cyber operations, espionage and information gathering, disruptive and destructive attacks, and geopolitical motivations with social media influence operations.
For anyone working in cyber security, the Iranian threat actor names are all too familiar - APT33 (Elfin), APT34 (Oilrig), APT 35 (Charming Kitten), APT39, CyberAv3ngers, and Muddywater, to name but a few. Moreover, the attributed malware families also resonate - Shamoon, Stonedrill, Chaos, Mahdi - with Shamoon infamously associated with the destructive attack on Saudi Aramco in 2012.
Who are they going after?
Iran focuses predominantly on infrastructure in other nations - energy, communications, healthcare, utilities, transportation, education, finance, government, and defense. In the current conflict, they will continue to target Israel and its allies to disrupt their capabilities in the conflict and diminish the strength of support. They will see this in both short-term and long-term strategic acquisition of leverage. They will no doubt ramp up their efforts on social media with disinformation and efforts to inflame opposition to supporting Israel.
What should organizations do now?
Since COVID-19, all organizations have significantly accelerated the implementation of digitization across their customers, suppliers, operations, and employees on new and expanded digital platforms. The risk from cyber threats to organizations therefore has never been higher. Geopolitical tensions and events increase risk, and organizations need to prepare and create resilience to the threat of an attack coming their way - either intentionally or as an unintended spill-over (think Wannacry).
Iran’s motives beyond data breaches have focused on disruption and destruction, and in the current conflict, these should be viewed as significant threats.
This is an intelligence-led approach, focusing on relevant threat intelligence about these threat actors and where they are operating, gathering their malicious indicators, and ensuring defenses stay up to date with blocking, detection, and response. This is about bonding the latest threat intelligence with security operations and maintaining strong situational awareness across the enterprise.
What is Anomali doing for customers?
Anomali released an Iran Cyber Activity dashboard to help customers do this. Coupled with Anomali’s Copilot AI suite, the Anomali Security Operations platform establishes the critical bonding of the latest relevant threat intelligence with an enterprise's security ecosystem of tooling, allowing security operations to maintain a strong defense and resilience.
The number of documented ransomware attacks in 2023 reached 4,368, a 55% increase from the previous year and a clearly concerning trend for the cybersecurity community. These nefarious acts compromise the integrity and confidentiality of sensitive data and present substantial financial and operational risks to organizations globally.
With cyber adversaries employing increasingly sophisticated attack methods, Security Operations (SecOps) teams face the daunting task of safeguarding critical assets against this menace.
Leveraging Threat Intelligence Sharing to Combat Ransomware
Ransomware adversaries deploy a myriad of tactics to infiltrate and compromise organizational networks. From phishing emails and social engineering to exploit kits and supply chain attacks, the attack surface is vast and varied.
What is concerning is the enormity of the problem. It is a prolific topic that comes regularly, and organizations should keep this in mind.
So, how can SecOps teams successfully navigate and mitigate these ever-evolving threats?
The first step is to gain insights into ransomware adversaries' tactics, techniques and procedures while bolstering your organization's resilience against attacks. Active participation in Information Sharing and Analysis Centers (ISACs) tailored to an organization's needs can achieve this. These centers play a pivotal role in assisting organizations with safeguarding critical infrastructure by collecting, analyzing, and sharing actionable threat intelligence among their members.
ISACs issue 24/7 threat warnings, provide incident reporting capabilities and empower members with tools for threat mitigation, ultimately enhancing overall resilience.
Another crucial step that enables proactive defense against ransomware is to deploy a purpose-built threat intelligence management platform tailored to your specific organization's specifications, which curates and enriches relevant raw data from hundreds of diverse sources of threat intelligence and provides real-time dashboards and machine-readable threat intelligence to help security teams quickly understand assess, prioritize, and proactively stop threats.
Integrate Ransomware Defense into Overall Risk Management
What should a ransomware prevention strategy look like? Ransomware protection strategies must align with an organization’s overall risk and compliance strategies. It cannot operate successfully in a siloed environment.
You need to know what critical assets and processes keep your business running and who or what protects those assets. Many companies need help identifying the assets they protect. This difficulty arises because vulnerabilities may exist in less obvious areas, such as back-end ordering systems, rather than in the most apparent ones.
Any part of the business operations could be vulnerable to cybercriminal attacks. Plugging those gaps is essential to prevent business disruption, financial loss, and regulatory censure.
Untangling the Complexity of Complying with Cybersecurity Regulations
Adhering to data protection regulations and those aimed at combating ransomware cyberattacks can be complicated, as laws and regulations can differ from state to state, federal jurisdictions, and internationally.
It is crucial to keep up-to-date with national security compliance regulations. However, it is vital to be aware that more states are creating their own regulations, which adds complexity for companies operating in multiple states, as each state may have distinct requirements, such as those for Texas and California. Although templates may be similar, subtle differences exist.
Additionally, international regulations differ from those in the US. Multinational companies operating abroad may unintentionally violate local laws and vice versa.
Using a platform that can identify and flag relevant regulatory concerns for your business is crucial for navigating the ever-changing landscape of cybercrime regulations. You can seamlessly align with your overall business policies by implementing robust cybersecurity compliance protocols.
Understanding Unique Frameworks and Vulnerabilities
In addition to general regulatory requirements, various sectors have specific frameworks and encounter distinct vulnerabilities. Breaches in these sectors can have profound consequences, extending beyond business operations to impact the public, national security, and financial markets.
Companies, particularly those within sectors with unique requirements, would benefit from adopting a cloud-native security solution. Such solutions offer tailored threat intelligence and can address sectors' unique threats and compliance needs like finance, healthcare, or government. Additionally, they provide scalability, rapid deployment, and integration capabilities, significantly enhancing an organization's resilience against ransomware.
The SecOps team needs the support of the business in adopting the right tools to manage and mitigate cyber threats. Businesses must prioritize security, recognizing its close connection to their operations. While there may not be a direct financial return on investments in security, neglecting it can lead to costly consequences in the event of a security breach. By investing in security measures, businesses can protect themselves and avoid potential financial losses.
Overcoming the Ransomware Challenges Using the Right Tools
A significant challenge faced by SecOps teams revolves around the abundance of false positives generated through automated processes within the security environment. Investigating each one is time-consuming, resource-intensive, and prone to human error.
The solution lies in leveraging tools capable of quickly discerning false positives and filtering out noise, allowing teams to focus efforts on genuine threats. After implementing Anomali solutions such as ThreatStream and the Security Analytics, companies have experienced many notable benefits.
For example, The Bank of Hope could more efficiently manage a substantial analytical workload, leading to savings on headcount while increasing overall capacity. Additionally, the reported false positive rates decreased significantly, reducing analysts' time chasing non-existent problems.
Blackhawk Network echoed similar satisfaction, stating that "Anomali enabled us to spend less time dealing with noise and more time focusing on critical issues."
Federal Systems Integrator (FSI) successfully integrated the ThreatStream solution seamlessly into various other cybersecurity tools in their environment and highlighted the support received from the Anomali team.
Anomali Your Best Defense Against Cyber Threats
"In the fight against ransomware, the best defense is one built on data and aligned properly to the threats a company faces." — World Economic Forum, 2023
As cybercriminals continuously refine their techniques to exploit vulnerabilities within organizations' systems, they wield many tools to breach defenses. For businesses, regardless of size, safeguarding assets remains an ongoing challenge, demanding a tailored and robust solution.
Such a solution should align with the intricacies of their operations, seamlessly integrate into existing systems, and be scalable to accommodate the expansion of their enterprise and the persistent evolution of threats.
Contact us today to request a demo on how we can help you safeguard your critical infrastructure against ransomware attacks.
In the evolving realm of cybersecurity, the development and implementation of robust threat models are the cornerstone of proactive defense strategies. Traditionally, this process has been shrouded in technical complexities, often requiring specialized expertise in structured query languages. However, a paradigm shift is underway as organizations embrace the intuitive power of natural language queries to build comprehensive threat models. In this blog, we explore the art of constructing cybersecurity threat models using natural language, with a particular focus on the role of User and Entity Behavior Analytics (UEBA) and the critical integration of these models with Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) capabilities.
The Rise of Natural Language in Cybersecurity Threat Modeling
Traditional threat modeling often demanded a deep understanding of complex technical structures, making it a domain accessible primarily to cybersecurity experts. However, the landscape of cyber threats is evolving, requiring an approach that empowers a wider audience, including non-technical stakeholders, to actively participate in the threat modeling process.
Advantages of Natural Language Queries in Threat Modeling
- Accessibility for All
- Traditional Approach: Threat modeling often involves intricate queries in specialized languages, limiting participation to those with technical expertise.
- Natural Language Advantage: Natural language queries democratize the process, allowing a broader range of stakeholders, including executives, risk managers, and compliance officers to actively contribute.
- Intuitive Understanding:
- Traditional Approach: Technical queries can be challenging to comprehend for non-technical stakeholders, leading to a potential gap in understanding.
- Natural Language Advantage: Natural language queries foster an intuitive understanding, breaking down the barriers between technical and non-technical teams.
- Faster Iterations:
- Traditional Approach: Technical queries might require constant iterations and revisions, leading to time-consuming processes.
- Natural Language Advantage: Natural language queries facilitate faster iterations, enabling agile responses to emerging threats and changes in the threat landscape.
Understanding UEBA: A Pillar of Intelligent Threat Modeling
User and Entity Behavior Analytics (UEBA) plays a pivotal role in enhancing the effectiveness of cybersecurity threat models. UEBA focuses on analyzing patterns of behavior to identify anomalies or deviations from established norms, offering a dynamic layer of defense against insider threats and advanced persistent threats.
Role of UEBA in Threat Modeling:
- Behavioral Anomaly Detection: UEBA excels in detecting deviations from normal behavior, allowing threat models to incorporate dynamic elements based on user and entity actions.
- Insider Threat Mitigation: By understanding typical user behavior, UEBA helps identify anomalies that may indicate insider threats, adding a layer of protection beyond traditional perimeter defenses.
- Continuous Monitoring: UEBA provides continuous monitoring capabilities, aligning seamlessly with the dynamic nature of threats. This constant vigilance enhances the accuracy and timeliness of threat model responses.
Example Use Case: Insider Threat Detection
Consider a scenario where a user, who typically accesses a specific set of files during regular working hours, suddenly attempts to access sensitive data at an unusual time. Traditional threat models might struggle to identify this anomaly, but UEBA, integrated with natural language queries, can dynamically adjust the threat model to flag and investigate this unusual behavior.
Integration with SIEM: Strengthening Threat Models with Real-time Visibility
The integration of threat models with Security Information and Event Management (SIEM) systems is crucial for achieving real-time visibility into an organization's security posture. SIEM platforms can aggregate and analyze security data from a broad range of sources, providing a centralized hub for monitoring and responding to security events.
Benefits of SIEM Integration:
- Centralized Data Repository: SIEM serves as a centralized repository for security data, providing a holistic view of an organization's threat landscape.
- Real-time Monitoring: Integration with SIEM enables threat models to have real-time access to security events, allowing for immediate responses to emerging threats.
- Correlation of Events: SIEM enhances threat models by correlating diverse security events, providing a contextual understanding of potential threats and their impact.
Example Use Case: Phishing Attack Response
Imagine a scenario where a phishing attack is launched, and multiple users across the organization report suspicious emails. Natural language queries integrated with SIEM can quickly identify patterns in these reports, enabling the threat model to dynamically adjust parameters for detecting phishing-related activities in real time.
SOAR Integration: Automating Responses for Enhanced Cyber Resilience
Security Orchestration, Automation, and Response (SOAR) capabilities enhance threat models by automating response actions to security incidents. SOAR platforms streamline incident response workflows, allowing organizations to respond swiftly and efficiently to cyber threats.
Advantages of SOAR Integration:
- Automated Incident Response: SOAR enables the automation of repetitive and time-consuming incident response tasks, freeing up security teams for more strategic activities.
- Workflow Orchestration: Threat models integrated with SOAR benefit from workflow orchestration, ensuring a coordinated and standardized response to security incidents.
- Reduced Mean Time to Respond (MTTR): SOAR integration contributes to a significant reduction in the Mean Time to Respond (MTTR) - from days to minutes, enhancing an organization's cyber resilience.
Example Use Case: Malware Detection and Remediation
In a scenario where malware is detected within the network, natural language queries can quickly identify affected entities. Integrated with SOAR, the threat model can automatically initiate a response workflow, isolating infected systems, notifying relevant teams, and launching remediation procedures.
Conclusion: Unifying Forces for Proactive Cybersecurity
In the dynamic landscape of cybersecurity, the synergy between natural language queries, UEBA, SIEM, and SOAR forms a formidable defense against an array of threats. The ability to construct and adapt threat models using intuitive language empowers organizations to foster a collective understanding of their security postures. As UEBA adds behavioral intelligence, SIEM provides real-time visibility, and SOAR automates responses, the holistic integration of these capabilities into a cohesive Security Operations Platform forms a proactive cybersecurity strategy that adapts to the evolving threat landscape. By unifying these forces, organizations can not only detect and respond to threats more effectively but also cultivate a resilient cybersecurity posture that stands firm against the challenges of the digital frontier.
Cybersecurity is in constant flux, influenced by technological advancements, geopolitical tensions, and the constantly increasing value of digital assets. A CISO's role is more critical and challenging than ever; safeguarding an organization's digital assets and complying with complex regulations demands vigilance and foresight.
A cornerstone of future-proofing cybersecurity lies in deeply understanding adversaries' evolving tactics, enabling CISOs to effectively anticipate and counteract sophisticated cyber threats.
This dynamic environment requires cybersecurity strategies that are not just reactive but proactively anticipate future trends and threats. An adaptive approach enables organizations to stay one step ahead of potential threats, ensuring their cybersecurity posture is robust, flexible, and forward-looking. Balancing these elements requires a comprehensive understanding of the current cybersecurity dynamics and a strategic approach to managing them.
Laying the Foundation for a Robust Strategy
Adaptive cybersecurity strategies are crucial as new threats increase in complexity and sophistication. Organizations must pivot from traditional, reactive security postures to proactive, intelligence-driven frameworks that not only detect but also anticipate and mitigate potential threats before they escalate.
This shift involves integrating cutting-edge technologies and analytics, enabling a deeper understanding of threat patterns and vulnerabilities. By fostering a continuous learning and adaptation culture, businesses can ensure their defenses remain robust and aligned with the latest security standards and practices. A future-proof cybersecurity strategy rests on several foundational elements:
- Legal and Compliance Standards Alignment: Ensuring regulatory compliance while maintaining security and efficiency.
- Risk Management: Implementing thorough vendor risk assessments and conducting regular in-house risk analyses to identify and mitigate potential vulnerabilities.
- Infrastructure Decisions: Choosing between cloud and traditional setups based on specific organizational needs and security considerations.
- Cybersecurity and IT Collaboration: Fostering a collaborative relationship between the cybersecurity team and IT departments to enhance asset management and security protocols.
Proactively Engaging Adversaries
An intelligence-led approach to cybersecurity emphasizes understanding adversaries' tactics, techniques, and procedures (TTPs). Organizations can develop a proactive defense mechanism by tracking the evolution of cyber threats and leveraging immediate threat intelligence. Incident management becomes more efficient, reducing the time from detection to response.
To improve proactive engagement with adversaries in cybersecurity, it's essential to understand attackers' tactics, such as Living Off the Land (LOTL) techniques. These strategies involve using legitimate system tools and processes for malicious purposes, allowing adversaries to blend into normal network activity and evade detection. This underlines the imperative for an intelligence-led cybersecurity operation, where real-time threat intelligence plays a pivotal role.
By harnessing the power of up-to-the-minute data on emerging threats and attacker methodologies, organizations can detect these subtle techniques and anticipate potential attacks before they happen. Such a proactive approach, informed by deep insights into adversary behaviors and tactics, enables the crafting of robust defense mechanisms that are not just reactive but are steps ahead of potential threats, ensuring a stronger and more resilient cybersecurity posture.
Innovating with Advanced Tools and Talent
The need for more skilled cybersecurity talent is a significant hurdle. Leveraging advanced detection and response tools and artificial intelligence can compensate for this gap, enhancing threat detection capabilities and enabling faster responses to incidents. This technological leverage is crucial in building a resilient cybersecurity framework. Ways to innovate with advanced tools in cybersecurity and how this supports talent include:
- Integration of Artificial Intelligence (AI) and Machine Learning (ML): AI and ML can quickly analyze vast amounts of data to identify patterns and anomalies that might indicate a potential threat or attack in progress. By automating the detection process and separating signal from noise, these technologies allow cybersecurity professionals to focus on more complex problem-solving and strategic planning tasks, enhancing their skill sets and job satisfaction.
- Implementation of cloud-native Security Information and Event Management (SIEM) tools: SIEMS are the inward-focused nerve center of Security Operations, and are critical in correlating external threat data to internal telemetry. A cloud-native SIEM also brings scalability that is beyond the reach of legacy SIEMS and is in line with existing big data processing requirements.
- Adoption of Security, Orchestration, Automation, and Response (SOAR) Tools: Automation reduces the manual workload on cybersecurity teams by performing repetitive tasks, while orchestration tools integrate various security processes and technologies to respond to threats more efficiently. This not only increases operational efficiency but also provides talent with the opportunity to engage in more meaningful, impactful work.
- Use of Advanced Threat Intelligence Platforms (TIP): These platforms provide real-time insights into emerging threats and adversary tactics, enabling cybersecurity teams to anticipate and respond to attacks proactively. Access to detailed threat intelligence supports talent development by keeping teams informed about the latest cybersecurity trends and attacker methodologies.
- Deployment of Next-Generation Endpoint Protection: Advanced endpoint protection solutions use behavioral analysis, exploit prevention, and other sophisticated techniques to detect and block threats. By equipping teams with cutting-edge tools, organizations can enhance their defensive capabilities and offer their cybersecurity talent challenging environments to develop their expertise.
- Enhancing Cloud Security with Advanced Configuration and Monitoring Tools: As organizations move to the cloud, advanced tools that provide visibility and control over cloud environments are critical. These tools support talent by enabling them to manage and secure cloud-based resources effectively, broadening their skill sets in cloud cybersecurity.
- Investment in Continuous Training and Education: Leveraging advanced tools requires a skilled workforce. Organizations can support their talent by investing in continuous education and training programs that cover the latest cybersecurity technologies and practices. This helps retain talent and ensures that the workforce remains at the forefront of cybersecurity innovation.
By innovating with advanced tools, organizations strengthen their cybersecurity posture and support the development and retention of their cybersecurity talent. A positive feedback loop is created by empowering and equipping skilled cybersecurity professionals with advanced tools, leading to improved security measures and driving further innovation in the field.
Incorporating these perspectives into security strategies alters the conventional response to digital threats, advocating for a proactive culture where every piece of intelligence is a step towards a more secure framework. This approach to security improves the ability to handle present dangers and lays the groundwork for anticipating and neutralizing future challenges.
It signifies a shift from static defense tactics to a dynamic, intelligence-driven model that prioritizes early detection and strategic foresight, ensuring that cybersecurity efforts are thorough, flexible, and in tune with the changing nature of cyber threats.
Best Practices for Operational Excellence
Operational excellence in cybersecurity hinges on consistently implementing foundational practices that bolster a proactive defense framework. Continuous observation of emerging threats enables organizations to maintain vigilance, identifying potential security issues before they escalate. This level of attentiveness guarantees that we promptly and knowledgeably respond to any unusual activity.
Alongside, actively seeking out nascent threats through systematic searches allows organizations to neutralize risks preemptively. This proactive stance elevates the organization's security measures and equips security teams with the knowledge to prevent adversarial successes.
Regular evaluations of potential vulnerabilities are crucial in reinforcing an organization's cybersecurity infrastructure. By systematically analyzing risks, organizations can effectively sequence their mitigation efforts, focusing first on vulnerabilities that pose the greatest risk. Continuous threat intelligence efforts enhance this systematic approach to risk management by providing valuable insights.
To achieve operational excellence in building a future-proof cybersecurity strategy, organizations should focus on several best practices that ensure their defenses are both robust and adaptable. These practices include:
- Continuous Threat Monitoring: Establish mechanisms for ongoing surveillance of the digital environment to detect threats as they emerge, which enables early identification and mitigation of potential security issues.
- Proactive Threat Hunting: Go beyond passive detection by actively seeking out indicators of compromise or vulnerabilities that adversaries could exploit. This approach helps in identifying and neutralizing threats before they can cause damage.
- Regular Risk Assessments: Conduct systematic evaluations to identify vulnerabilities and assess their potential impact on the organization, allowing for prioritized and informed decision-making regarding mitigation strategies.
- Adherence to Security Patch Management: Maintain a rigorous schedule for updating and patching systems and software. Keeping technologies up to date is critical in protecting against known vulnerabilities and exploits.
- Integration of Real-time Threat Intelligence: Use up-to-date threat intelligence to inform security strategies and operational tactics. This intelligence can guide proactive measures and enhance the organization's ability to respond swiftly to emerging threats.
- Incident Response Planning: Develop and regularly update incident response plans to ensure quick and effective action during a security breach. This includes clear roles and responsibilities, communication plans, and recovery procedures.
- Training and Awareness Programs: Foster a culture of security awareness within the organization through regular employee training and educational programs. This helps recognize potential security threats and reduces the risk of insider threats.
- Collaboration and Sharing: Engage in information sharing with industry peers and participate in relevant security communities. Collaboration can provide insights into new threats and best practices, enhancing collective security posture.
- Leveraging Advanced Security Technologies: Invest in and deploy advanced security solutions such as AI and machine learning tools for anomaly detection, automation of routine tasks, and enhanced analysis capabilities.
- Strategic IT and Cybersecurity Alignment: Ensure the full integration of cybersecurity strategies with IT operations and business objectives. This alignment ensures that security measures support organizational goals without impeding operational efficiency.
Integrating these measures with continuous monitoring and systematic threat detection fosters a comprehensive defense strategy. By adopting vital operational practices, an organization can ensure its cybersecurity strategy remains robust against increasingly complex threats, safeguarding its operations from present and future cyber dangers.
Empowering Strategies with Anomali
Anomali's intelligence-driven solutions are pivotal in enabling efficient threat identification and mitigation. The platform's capabilities in enhancing threat intelligence, incident response, and risk management illustrate Anomali's contribution to strengthening organizational cybersecurity resilience. Success stories from various deployments underscore the tangible benefits of integrating Anomali's solutions into a cybersecurity strategy.
Adaptability and continuous improvement are the keys to building a future-proof cybersecurity strategy. As threats evolve, so too must the strategies to combat them. CISOs are encouraged to take immediate action to enhance their cybersecurity posture, leveraging insights, best practices, and Anomali’s innovative solutions. With the right approach and tools, one can successfully navigate the ongoing journey towards achieving cybersecurity resilience.
Cybersecurity threats are (unfortunately) endemic, and accelerating not only in terms of volume but also sophistication. Security teams are constantly slammed with Indicators of Compromise (IOCs) that are increasingly subtle and require abilities to process that are 1) potentially urgent, and 2) often beyond the reach of even experienced security analysts. Security Operations Centers have been pushing hard on this challenge for years, but are often hampered by legacy technologies that were designed for a very different environment. The good news? Cloud-scale and AI-enabled security solutions are entering the market at a perfect time.
In the pursuit of cybersecurity resilience, Artificial Intelligence (AI) is revolutionizing how organizations interpret and respond to IOCs. One of the most impactful applications of AI is the generation of immediate executive-level summaries for IOCs. This blog explores the advantages of employing AI to correlate external threat intelligence with internal telemetry and log file analysis. It’s an innovative strategy that benefits analysts by providing comprehensive summaries tailored for both executive leaders and frontline practitioners.
The Imperative of Swift and Insightful IOC Interpretation
Cyber threats are evolving at an unprecedented pace, requiring organizations to strengthen their defenses with adaptability, speed, and precision. IOCs, such as suspicious network activities, malware signatures, or anomalous user behavior, serve as critical breadcrumbs that can lead to the identification of potential security incidents. However, the challenge is to accurately interpret these indicators as fast as possible to mount effective responses.
Traditional IOC Interpretation has challenges with information overload and the need for effective communication:
- Information Overload: Analysts often grapple with 1) a deluge of data from internal telemetry and log files, and 2) data that is often dense, complex, and extremely detailed (the opposite of the information needs of the C-suite) making it challenging to quickly separate signal from noise and report meaningful information to people who need a strategic assessment in a hurry—leading to our next point.
- Executive communication: Execs need two data points: what happened, and are we at risk? Translating technical details into actionable business insights for executive leaders is a time-consuming process (and not something where you want mistakes slipping through), delaying decision-making and an effective, timely response.
AI-Driven Executive Summaries: Unlocking Operational Efficiency
Artificial Intelligence, particularly in the form of Natural Language Processing (NLP) and machine learning algorithms, has become a game-changer in addressing the challenges of IOC interpretation. By harnessing AI capabilities, organizations can take detailed, low-level technical data and generate immediate executive-level summaries that distill the essence of IOCs into business or strategic terms, enabling faster decision-making and threat remediation.
Advantages of AI-Generated Executive Summaries:
- Rapid Insight Extraction: AI algorithms can immediately analyze and correlate IOCs from diverse sources, distilling critical insights for prompt, accurate decision-making (seconds vs. hours across petabytes of data).
- Executive Communication: Through the use of natural language queries, analysts can generate detailed responses without the need to be fluent in query languages (of which there are many, and usually vendor-specific). When coupled with generative AI solutions such as Anomali Copilot, this can be used to immediately generate summaries that will make sense to executive decision-makers, by translating technical details into business-level actionable insights.
- The Power of Correlation: External Threat Intelligence Mapped to Internal Telemetry
Effective cybersecurity demands a holistic understanding of the threat landscape, encompassing both external threats and internal vulnerabilities. Correlating external threat intelligence with internal telemetry and log file analysis enriches the context of IOCs, providing a more nuanced and cohesive view of potential risks.
Advantages of Correlation:
- Contextual Relevance: External threat intelligence contextualizes IOCs, helping organizations discern whether an indicator aligns with known attack patterns that are relevant to their internal attack surface. In other words, does this threat apply to us, and if so, exactly where?
- Proactive Defense: Correlation enhances the ability to proactively defend against emerging threats, identifying potential risks before they manifest. Once a threat is identified and correlated, messages can automatically be sent to relevant security tools (such as firewalls) that enable them to block IOCs with specific profiles.
AI: Addressing the Need for Speed
The synergy of AI-driven analysis and interpretation brings a new dimension to IOC management. This enables organizations to stay ahead of evolving threats and fortify their defenses with a proactive mindset.
Applying AI to the Correlation Process:
- Automated Pattern Recognition: AI identifies patterns in vast datasets of IOCs, distinguishing normal activities from potentially malicious behaviors. We’re talking about analyzing petabytes of data in seconds, not hours or days.
- Understanding a Dynamic Threat Landscape: Machine learning adapts to the dynamic threat landscape, ensuring that correlation remains effective in the face of continuously evolving and potentially large-scale attack tactics.
- Reduced False Positives: AI-driven correlation also minimizes false positives, separating signal from noise and focusing analysts' attention on genuine threats and streamlining response efforts.
Real-World Use Cases: Putting AI to the Test
The efficacy of AI-generated executive summaries can be illustrated in real-world scenarios where organizations leverage these capabilities to strengthen their cybersecurity postures.
Use Case 1: Swift Response to Phishing Campaigns
A sudden surge in suspicious emails triggers AI algorithms to correlate indicators with known phishing patterns. Executive leaders receive a high-level summary outlining the potential risk to the organization, while frontline practitioners receive detailed technical information for immediate response. And all of this happens in minutes, rather than hours or days.
Use Case 2: Are we at risk?
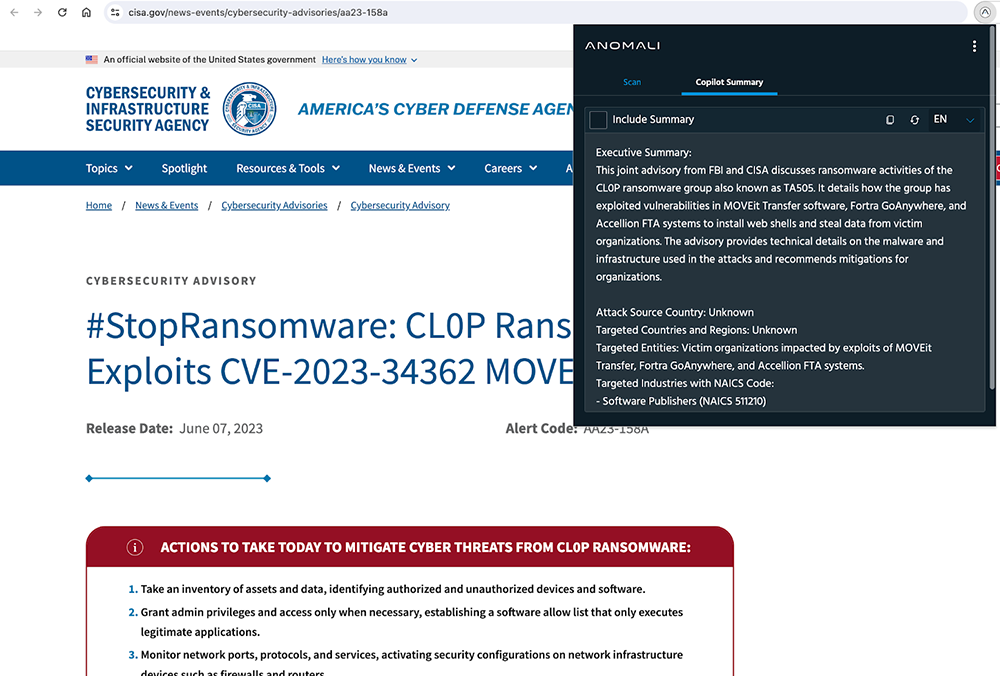
CISA releases an advisory on newly discovered TTPs and IOCs related to ransomware activity (which happens pretty much continuously). The C Suite (which has begun paying much closer attention to security risks) immediately wants to know if this presents any risk to the organization. Using AI correlation and summarization, not only can you provide a nice, concise summary of the risk (summarize 40 pages of dense technical information into a one-pager, in under a minute), but you can also generate a report of where exactly in your IT infrastructure there is a risk of exposure. Executive leaders receive an immediate summary of the event's potential impact, while practitioners receive actionable guidance on isolating suspicious users and the affected systems, and launching an investigation. This type of detection/investigation/remediation event used to take days (if you were lucky). Now it can be done in minutes.
Use Case 3: Keeping your analysts from running out the door
T1 and T2 analysts are often tasked with the tedious and mind-numbing task of interpreting and prioritizing hundreds of IOCs per day, where processing just one event can take 20-30 minutes. Most of this is noise, not signal, and is an ideal use of AI technology. By letting AI applications grind through the minutia of random events, your analysts can uplevel their threat program performance and work on genuine threats.
Conclusion: Empowering Cybersecurity with AI-Driven Insights
The application of AI to generate immediate executive-level summaries for IOCs stands as a testament to the transformative power of technology. By harnessing the capabilities of AI-driven correlation, organizations can distill complex technical details into actionable insights for executive leaders and frontline practitioners. This not only saves analysts a significant amount of time and effort (with its associated cost savings), it accelerates decision-making and empowers analysts to focus on strategic analysis and proactive threat hunting. As organizations navigate the intricate web of cyber threats, AI is quickly emerging as a trusted copilot, providing the speed, precision, and clarity required to instantly fortify your security posture in the face of a highly dynamic security landscape.
In the nonstop turbulence that characterizes cybersecurity, Chief Information Security Officers (CISOs) play a pivotal role in piloting their organizations through an increasingly sophisticated array of threats. One of the most critical components in their arsenal is the Security Information and Event Management (SIEM) system. SIEMs are the central nerve centers that aggregate, analyze, and correlate security data from various sources to quickly detect and respond to threats. However, to stay ahead of adversaries and mitigate potential breaches, CISOs must understand the need for real-time speed in log queries and the ability to support unlimited lookbacks across all internal telemetry correlated to external threat data.
The challenge of real-time speed
Milliseconds matter when it comes to detecting and responding to security incidents. Attackers are relentless, increasingly subtle/sophisticated, and move swiftly to infiltrate an organization’s network, exfiltrate sensitive data, or launch damaging attacks. To effectively counter these threats, CISOs need a SIEM system that can process and query log data in real-time and at scale.
Data Volume and Velocity: Organizations generate vast amounts of log data from various sources, including firewalls, intrusion detection systems, and endpoint devices. This data must be ingested, parsed, and analyzed in real-time to separate signal from noise, identify anomalies, and prioritize potential threats. Being able to immediately identify subtle patterns in large data sets and draw prioritized correlations is an area where AI-enabled SIEMs should excel.
Advanced Threats: This is not just about processing a high volume of incidents. Zero-day exploits, and APTs (Advanced Persistent Threats) can often deliver sophisticated multifaceted attacks that require immediate attention. A SIEM that can immediately identify significant threat patterns of behavior to deliver a holistic view (from threat intelligence through to the Security Operations Center) of real-time query results enables security teams to respond promptly and in context to emerging threats, minimizing potential damage.
Operational efficiency: Real-time log query capabilities enhance the efficiency of security operations. Analysts can immediately identify false positives, investigate incidents, make informed decisions, and quickly distribute critical information where it is needed (e.g. telling firewalls to block messages with a specific profile), reducing the mean time to detect and respond.
Achieving real-time speed in log queries involves several considerations:
Scalability: The SIEM platform should be capable of scaling horizontally to handle the increasing volume and variety of log data generated by the organization, particularly when dealing with multiple, distributed log sources. Dynamic scalability also requires automated load-balancing to avoid performance bottlenecks and facilitate the prioritization of critical security events. This is particularly important given the complexity and distributed nature of both IT and OT systems.
Data Ingestion Optimization: Given the volume of data being ingested in a SOC, correlating real-time (or streaming) analytics to the external threat environment allows security teams to analyze and act on contextualized security events as they occur. Working from a cloud-native (and serverless) architecture also allows SOCs to instantly scale resources on demand, while lossless compression algorithms can help reduce data storage requirements without compromising integrity. Efficient log data ingestion mechanisms, such as log shippers can also minimize delays in processing and indexing incoming data.
Indexing and search optimization: Query languages are complex, often vendor-specific, and require years of experience to develop proficiency. Advanced indexing and search algorithms using an NLP-based interface are quickly becoming table stakes for accelerating query performance. Techniques like caching or parallel processing can also significantly enhance the speed of log queries. The SIEM system must also provide efficient search and retrieval mechanisms for historical data, enabling analysts to retrieve information quickly. Ideally within seconds across petabytes of data.
Machine learning integration: The volume of incidents that need to be processed (with all the multiple steps involved) is well past any human’s ability - and has been for years. Leveraging machine learning models for anomaly detection and threat scoring across hundreds of thousands or millions of incidents in real time can enhance the SIEMs' ability to identify emerging threats quickly. As AI is rapidly adopted across the industry, this is becoming a standard operating procedure for most organizations.
Unlimited lookbacks: a strategic necessity
While real-time speed is crucial for handling immediate threats, the ability to support unlimited lookbacks across internal telemetry and correlate this to external threat data is equally vital for comprehensive threat analysis, historical context, and compliance requirements.
Historical analysis: Cybersecurity incidents often involve long, complex attack chains spanning weeks or months. To understand the full scope of an incident and identify its origins, CISOs need the ability to look back at historical data. The normal lookback period for most SIEMs is 90 days, while the actual scope of an event can easily go back well past that. Without unlimited lookbacks, critical pieces of the puzzle may be missing. This is also a core component of data storage and retention policies. Implementing and enforcing a robust data retention policy (which is likely to vary by industry) combined with cloud-scale storage solutions is essential for maintaining historical log data.
Compliance and Auditing: Many industries and regulatory bodies require organizations to retain security data for extended periods. Compliance audits often require the ability to review historical logs to demonstrate adherence to security standards and incident response procedures. Rather than sending your auditors on a snipe hunt, a properly configured SIEM can generate historical audit trails on demand. This is particularly useful for non-optional short timeframe-sensitive compliance mandates like SEC Form 8K.
Threat Intelligence integration: Threat intelligence feeds can include indicator-based, vulnerability-based, campaign (TTPs) or attribution-based, OSINT, and even Dark Web data, providing valuable information about emerging threats. The ability to correlate historical data with threat intelligence feeds can help organizations proactively defend against known attack vectors. This takes the question “Who is attacking us?” and extends it to “And where exactly are we exposed to this particular threat?”.
Striking the right balance
CISOs face the challenge of striking the right balance between real-time speed and unlimited lookbacks. While real-time capabilities are critical for immediate threat detection and response, the ability to access historical data is equally essential for comprehensive threat analysis, compliance, and long-term security strategy.
Tiered data storage: One strategy to address this challenge is implementing tiered data storage. Real-time data can be stored in high-performance storage systems, while historical data can be moved to cost-effective, long-term storage solutions. Or, as an alternative:
Datalake: Ideal for large volumes of raw diverse data that will be subject to analytics, and offers better flexibility for a broad range of data types without the need for upfront structuring. If you plan to throw AI (specifically LLMs) at large data sets, this is a good option.
Retrospective analysis: CISOs should encourage their security teams to conduct retrospective analysis of historical data periodically. This practice (particularly around dark data) involves revisiting historical logs to uncover previously undetected threats or patterns that may have gone unnoticed.
Incident response playbooks: Developing automated incident response playbooks that incorporate both real-time and historical data analysis can help streamline and accelerate response efforts for various types of incidents.
Conclusion
CISOs must recognize the strategic imperative for real-time speed in log queries and the ability to support unlimited lookbacks across all internal telemetry and external threat data. Real-time capabilities are vital for immediate threat detection and response, while unlimited lookbacks empower organizations to conduct comprehensive and contextualized threat analysis, meet compliance requirements, and strengthen long-term security strategies.
To achieve these objectives, CISOs must collaborate closely with their security teams and SIEM vendors, continually assess their SIEM architectures' scalability and performance, and implement robust data management and storage strategies, By striking the right balance between real-time speed and unlimited lookbacks organizations can bolster their cyber security posture and stay one step ahead of evolving threats in an increasingly digital world.
As digital threats continue to grow in both volume and sophistication, a striking statistic from ISACA's 2023 State of Cybersecurity report reveals that 48% of organizations have seen an uptick in cyberattacks compared to the previous year. This significant increase highlights the imperative for robust, adaptive cybersecurity strategies. Central to these strategies is the role of the SIEM, a key component in the security toolkit of Chief Information Security Officers.
SIEMs are transcending their traditional defensive role, emerging as a strategic enabler of cybersecurity measures. As a CISO, you can optimize your SIEM to reinforce your organization's security defenses and demonstrate the effectiveness and ROI of cybersecurity efforts to leadership and stakeholders.
In cybersecurity, where threats are multifaceted and relentless, SIEMs stand out as a critical technology for strengthening defenses and communicating their value. It embodies an essential asset in the CISO's arsenal against digital threats.
The Essential Role of AI-powered SIEM in Cybersecurity
A SIEM's contribution to cybersecurity extends well beyond traditional log storage, search, correlation, and compliance reporting. It also integrates data collection and log management, offering a full-spectrum view of an organization's security health. This is key for tackling the complexities of modern cyber threats.
SIEM solutions today must offer rapid access to stored historical data (multiple years, not a few months), while delivering correlations for effective threat hunting and swift data searches, ensuring a comprehensive understanding of security incidents. This capability mitigates the limitations of legacy systems such as slow query processing and lookback constraints which are inadequate in addressing the rapid expansion of digital footprints and sophisticated cyber threats.
Modern SIEM solutions are primarily cloud-native offerings that significantly advance speed, scale, and the ability to correlate external threat data with internal telemetry. These offerings have better ease of use, and the integrations necessary for an effective data-driven security strategy. They empower security teams to focus on strategic tasks, thus improving detection, response, remediation, and overall cybersecurity resilience.
Advancing Threat Detection and Response Capabilities through SIEM
Modern SIEM solutions - especially those powered by AI - incorporate advanced analytics and a nuanced approach to threat detection. They excel in providing a deep and comprehensive analysis of threats, extending beyond the traditional scope of SIEM. These systems integrate many intelligence sources, including global threat feeds and internal data, to offer a multidimensional perspective on security threats. A holistic approach is vital in detecting known, emerging, and sophisticated threats legacy systems might miss.
Integrating machine learning and artificial intelligence in SIEM solutions enhances their predictive capabilities, enabling the automation of previously manual tasks to accelerate the identification of anomalies that could indicate potential security incidents. This forward-thinking approach is vital for proactive defense, allowing organizations to take preemptive measures against threats before they develop into significant breaches.
Contextual information plays a pivotal role in the effectiveness of SIEMs in threat detection. Modern SIEM solutions do more than identify anomalies; they provide context-rich insights that aid security analysts in understanding a threat's nature, origin, and potential impact. This depth of information is crucial for informed decision-making regarding threat mitigation and response strategies.
The advancement of threat detection through modern SIEM solutions is characterized by comprehensive analytics, extensive integration of intelligence, predictive capabilities, and a focus on contextual analysis. These features empower security teams with robust tools to identify and respond to potential security threats with heightened speed and precision.
Optimizing Threat Response with SIEM
SIEM solutions excel in streamlining threat response. They automate security data analysis, enabling quicker remediation of threats. AI-driven SIEM solutions have often shown a marked improvement in threat response times, bolstered by their efficient data processing and real-time analysis capabilities.
SIEM solutions integrate with third-party threat intelligence feeds, which help teams block or detect new attack signatures. This integration enables faster and more accurate identification of threats and accelerates the incident response process.
Fortifying Security Posture via SIEM
Continuous monitoring and analytics are crucial in reinforcing an organization's security posture. SIEMs aid in this by offering ongoing insights and compliance management, thus reducing overall organizational risk. Modern SIEM solutions exemplify this, providing an overarching view of security health, and ensuring compliance with various regulatory standards.
Aligning Cybersecurity Strategies with Business Goals
One key challenge CISOs face is aligning cybersecurity strategies with business goals. The SIEM can play a pivotal role in this process. By providing a current, comprehensive view, the SIEM can help you identify areas where your cybersecurity strategies can better align with business objectives.
For instance, by reducing the risk of data breaches and ensuring compliance with data protection regulations, your cybersecurity efforts can support the business goal of maintaining customer trust and enhancing brand reputation.
Calculating and Communicating the Value of Cybersecurity Investments
One of the main challenges faced by CISOs is clearly articulating the importance of cybersecurity and the value derived from tools such as SIEMs. It's not just about presenting raw data; it's about translating it into business language that executives and board members can understand and act on.
First, highlight the cost savings. SIEM is always considered a cost burden. However, the implementation of a SIEM solution helps reduce the costs associated with data breaches by improving threat detection and accelerating response times, thereby minimizing potential damage.
Second, emphasize the role of the SIEM in maintaining regulatory compliance. Many industries are governed by regulations that require specific security or data privacy measures. Non-compliance can result in hefty fines, legal action, and reputational damage. SIEM solutions can help ensure you remain compliant, saving your organization from these potential pitfalls.
Finally, demonstrate strategic value. SIEM solutions provide a wealth of data that can be used for strategic decision-making. For example, understanding the types of threats your organization faces can inform resource allocation and investment decisions.
Calculating the ROI for cybersecurity can be challenging due to the intangible nature of its benefits. However, there are several ways to quantify the value of your cybersecurity investments.
One method is to compare the cost of potential data breaches with and without a SIEM solution. According to the National Institute of Standards and Technology (NIST), the average cost of a data breach is orders of magnitude higher than the cost of implementing a SIEM solution.
Another method is to calculate the cost savings from improved incident response times. SIEM solutions enhance incident response capabilities, reducing the time and resources needed to respond to IOCs and IOAs. The value of maintaining regulatory compliance can also be factored into ROI calculations. As mentioned earlier, non-compliance will result in significant financial penalties.
The Strategic Importance of SIEM for CISOs with Anomali
SIEMs hold a strategic position in a CISO's toolkit. It's not just a tool for managing threats but a means of advocating for necessary cybersecurity resources and budget allocations. Aligning SIEM data with business objectives is crucial in demonstrating how cybersecurity strategies contribute to the organization's broader goals.
SIEMs also present a powerful solution for CISOs looking to enhance their cybersecurity posture and effectively communicate its value. As the threat landscape keeps getting complex and evolves, the modern SIEM remains a constant ally for CISOs in safeguarding their organizations. Look for SIEM solutions that provide clear, actionable insights that can help you demonstrate the value of your cybersecurity investments and align your cybersecurity strategies with your organization's business objectives. Please contact us today to learn more about how Anomali can help you achieve the security objectives we’ve outlined.
Anomali is announcing a significant expansion of its existing offering for enterprise security teams. We have a long and established presence in the threat intelligence domain with our market-leading ThreatStream platform, and today we are introducing an AI-Powered Security Operations Platform that combines SIEM, SOAR, and TIP advanced functionality to deliver on use cases for the SOC analyst, CTI analyst, and threat hunter.
The Anomali Security Operations Platform combines the largest threat intelligence repository in the world with the industry’s fastest, most scalable, intelligent SIEM. This integrated solution enables Anomali to deliver near real-time correlations at petabyte scale with threat-driven insights across identity, endpoint, network, cloud, and email detections. This release also includes the formal release of Anomali Copilot. Specific components of this product release include:
- Anomali Copilot
- Updated SIEM functionality
- Updated SOAR functionality
- Updated Dashboard/UI
- Network Analytics
- Endpoint Analytics
Anomali Copilot enhances the speed and efficiency of incident response by cybersecurity analysts. Incorporating Anomali Copilot’s generative AI into the Anomali Security Operations Platform significantly accelerates performance across all systems resources. Enabling Anomali to, for example, search petabytes of data in seconds, instead of the current legacy standard of hours or days to run a search - assuming the search doesn’t time out.
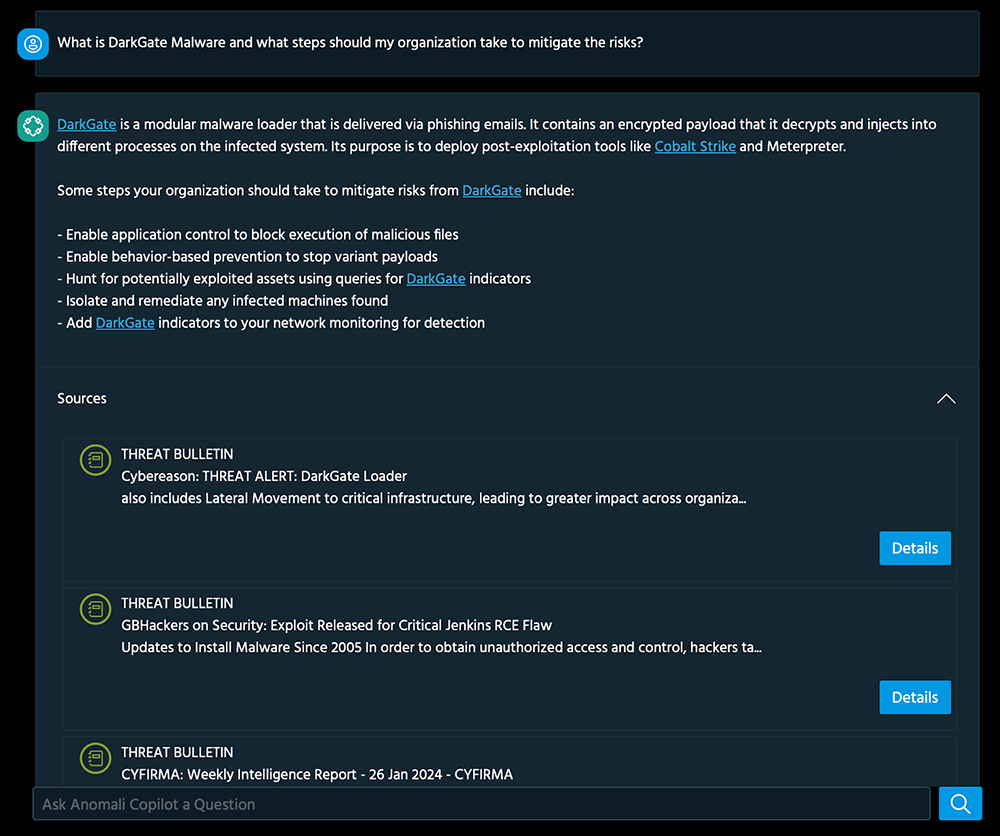
Enhance Cyber Threat Visibility and Analyst Efficiency with Anomali Copilot's AI-enabled Platform
Businesses can immediately and comprehensively extend their visibility into cyber threats across the entire organization using Anomali Copilot’s generative AI enablement. Copilot uses cybersecurity-specific large language models to understand suspicious activities, with orders of magnitude improvements in speed and accuracy.
Anomali Copilot helps analysts save time with summarization capabilities across the platform, supported by real-time chat about intelligence specific to the analyst’s organization. Copilot is also used in event search AQL (Anomali Query Language) generation, ingestion, and summarization. This includes a real-time NLP chat interface with intelligence-backed responses, a semantic search for related content, and multi-language support. The analyst effectively has sophisticated help available from an AI engine that is always available. Data is securely stored and transmitted and is never used to train AI datasets.
Anomali Copilot’s browser plug-in identifies potential threats or security risks. It provides an immediate and comprehensive perspective on threat activity using natural language processing (NLP) to analyze and interpret large amounts of data from various sources within ThreatStream and other sources. Copilot uses NLP to interpret text from blogs, forums, and social media to identify threat actors and potential future threats. A dense, 40-page technical document can be processed in seconds into a short summary, prepared for either executive leadership or practitioners.
Phishing detection becomes easier with NLP. Anomali Copilot can analyze emails and other communications to identify phishing attempts. It can analyze the language used in an email to identify potential red flags that indicate a phishing attempt, including urgency, requests for personal information, or other suspicious language.
SIEM functionality
Beyond making data ingestion fast, simple, and cost-effective storage, this release includes incident management capability to dive deep into investigations and responses, all while mapping every detection to MITRE TTPs to ensure comprehensive threat coverage. This capability will introduce over 1,000 different detections across all log types, supported by alerts with multiple integrations. Detections can also be risk-scored (automatically or manually) and aligned to the MITRE ATT&CK framework while supporting detections across a broad range of log types.
SOAR Capability
This release will also amplify the effectiveness of threat detection and response efforts through the integration of threat intelligence with Security Orchestration, Automation, and Response (SOAR). Anomali’s SOAR capability is not bolted on but instead meticulously built from the ground up, bringing unparalleled automation and efficiency to security operations.
Designed to scale with any organization's automation and response needs, our new SOAR functionality allows the creation and execution of actions via query language syntaxes/natural language, enabling highly customizable responses to security incidents. Faster and more informed decision-making is supported by the seamless enrichment of threat data via ThreatStream and VT/Shodan/AbuseIPDB.
Incident response is improved by automating ticketing processes, which reduces manual overhead and ensures tickets are tracked and resolved promptly. Our goal is not just improving response, but to help with remediation.
UI/Dashboarding function
Customers can view their security landscape holistically through dynamic visualization that highlights key metrics and trends. This allows the transformation of raw data into meaningful insights that can immediately identify threats and security vulnerabilities while monitoring compliance. This also fosters improvement in communication and decision-making by allowing the sharing of these AQL/NLP-powered customized dashboards among team members and stakeholders.
Endpoint Analytics
This capability delivers immediate visibility and action on anomalies, reduced dwell time, improved accuracy to minimize false positives and negatives, comprehensive analysis to uncover hidden patterns, and enhanced forensics to aid post-attack analysis. Anomali’s endpoint analytics feature provides continuous real-time threat detection by monitoring endpoint telemetry across the organization. Machine Learning powers our endpoint analytics to assess file hash risks for proactive threat detection. This delivers detailed insights into the threat nature and severity beyond binary classification (malicious/not malicious) for incident prioritization. Overall, this new feature enables customers to improve the accuracy of endpoint detections to minimize false positives and perform a comprehensive analysis to uncover hidden patterns within data.
Network Analytics
Our new network analytics feature continuously analyzes flow data to deliver comprehensive insights into east-west network traffic patterns, monitoring, and alerting on threats as they happen. The solution takes an "inside out" approach rather than focusing solely on external threats. Anomali network analytics scrutinizes internal traffic to look for hidden threats/lateral movement/zero-day exploits across all network telemetry.
How do SOC teams benefit from this release?
An Anomali Security Operations Platform that combines SIEM, SOAR, endpoint/network analytics, and AI will address several key security issues:
- Data overload: The non-stop volume of security data entering any system increases storage costs and hampers the analyst's ability to process critical events quickly. AI-driven analytics helps analysts detect anomalies faster and more efficiently, and quickly surface and action the highest priority threats.
- Slow response: Manual processes and complex workflows slow investigation and containment of threats, andSOAR-enabled automation accelerates a more cohesive and effective response.
- Skills shortage: Lack of cybersecurity talent makes it hard to protect organizations from the increasing number and sophistication of threats. The augmentation delivered by Anomali Copilot allows small teams to achieve more in a shorter time frame. This isn’t about working harder, it's about being more efficient.
- Limited visibility: Siloed tools only provide partial visibility. Customers can now have comprehensive, real-time contextual monitoring by providing an AI-driven dashboard that enables unified analytics and data aggregation.
- Compliance risks: Inability to prove diligence across security data against standards like SEC Form 8K, HIPAA, or PCI DSS can often lead to non-trivial fines (not to mention a very public faceplant). Anomali’s immediate and detailed reporting can reduce responding to compliance mandates from days/weeks to minutes.
Anomali now offers the industry’s only SIEM that fully leverages and integrates unmatched threat intelligence capabilities, and we have a significant advantage in making AI-powered Security Operations a reality for SOC teams. By combining Anomali’s understanding of both IoCs and IoAs during the detection and investigation process, Anomali’s Security Operations Platform is set to exceed current market offerings.
Current SIEMs also struggle to solve the analyst’s pain point of identifying key information and intelligence around internal assets, meaning hostnames, identities, etc. By adding asset intelligence scanning into the Copilot product alongside threat intelligence scanning, an analyst can quickly deduce whether an IP, hostname, or identity exists inside their security analytics logs. The scan can produce asset or identity surveillance, reports, and insights allowing for faster detection and investigation triage and removing the first 10-20 minutes of an analyst attempting to answer the question, “What is this IP/asset/user and how critical is it?”
Anomali's Enhanced SIEM Functionality for Next-Level Security Operations
With its latest release, Anomali has increased its Security Operations Platform by introducing enhanced SIEM functionality. This advanced capability enables businesses to tackle the challenges of data overload, slow response times, limited visibility, and compliance risks head-on.
By leveraging AI-driven analytics, Anomali's SIEM functionality empowers analysts to detect anomalies rapidly, automate processes through SOAR, gain comprehensive and real-time visibility, and easily ensure compliance. Anomali's commitment to delivering cutting-edge SIEM functionality is revolutionizing security operations and paving the way for proactive threat detection and incident response.
This release is a game-changer for both Anomali and the industry we serve. We’re expanding our market-leading presence in Threat Intelligence into the Security Operations domain with a very competitive solution that directly addresses pain points that are both broad and deep. Don't miss out on the opportunity to learn more about our product! Contact us now to schedule a demo and see how it can transform your business.
We are excited to announce the launch of Anomali Copilot, our suite of generative AI solutions designed to revolutionize the way Security Operations Centers (SOCs) detect, investigate, and respond to incidents and alerts. With Copilot by your side, your SOC will be supercharged in its mission to safeguard your organization from cyber threats.
Security teams and CISOs are being asked to do more with less. While the threats are increasing and getting complex, CISOs face challenges in hiring skilled cybersecurity talent that is efficient in addressing these threats. To add to this, there is tremendous pressure on the security team to cut costs. Automation of the workflows and assisting in addressing the changing threat landscape by leveraging the enhancements in AI provides a new way to address the talent gap, and rising costs while getting easier and better insights into threats.
Cybersecurity professionals and organizations striving to enhance their security posture should be particularly interested in Anomali Copilot. Whether you're a security analyst, threat intelligence professional, or SOC team lead, Anomali Copilot will become your indispensable ally in navigating the complex landscape of cyber threats. With Anomali Copilot's AI-powered assistance, you can amplify your capabilities, increase efficiency, and drive faster and smarter decision-making.
Detect, Investigate, and Respond with Confidence
Anomali Copilot leverages the industry’s largest threat repository (ThreatStream), is built on a secure and private foundation of AI models, and is an integral part of the Anomali Security Operations Platform. By harnessing the power of generative AI, Anomali Copilot addresses the critical challenges faced by security teams, empowering them to streamline their efforts and stay one step ahead of evolving threats.

Streamlined Summarization
With Anomali Copilot, you can say goodbye to information overload. Generative AI excels at processing vast amounts of data, condensing it into key insights and actionable intelligence. From complex threat models to news articles, Anomali Copilot will swiftly summarize the key takeaways, enabling you to focus your efforts on containment and response.
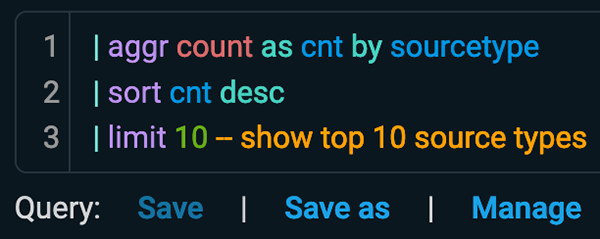
Effortless Natural Language with AQL
You don't need to be an expert in query languages to gain valuable insights from your data. Anomali Copilot simplifies the process by translating your queries into Anomali Query Language (AQL), allowing you to generate dashboards and alerts in seconds. And if you’re already a ninja in another query language, Anomali Copilot will assist you in translating your detections effortlessly.
Seamless Chat Experience
Engage in conversations with an expert threat intelligence advisor who understands the unique needs of your organization. Anomali Copilot enables you to use natural language to interact with your threat intelligence, providing you with answers backed by verified sources and searches. Whether you need guidance, best practices, or quick access to information, Anomali Copilot will be by your side.
Empowering MITRE Attack Flow Automation
Anomali takes pride in our collaboration with MITRE concerning Attack Flow analysis. Anomali Copilot leverages this partnership to automatically analyze and create Attack Flows, saving you precious time and resources. By applying these insights to your alerts and detections, you can prevent harmful events before they occur, bolstering your proactive defense strategy.

Anomali Copilot complements and accelerates your SOC Analysts
Anomali Copilot represents another milestone in our commitment to continuously innovate and push boundaries in the field of cybersecurity. By incorporating generative AI technology into our product offering, we aim to equip security teams with advanced tools to combat the ever-evolving threat landscape effectively. Anomali Copilot is just the beginning of our journey to transform the cybersecurity industry, and we invite you to join us as we shape the future together.
Learn more about Anomali Copilot and schedule a personalized demo today!
Dark Data. Sounds kind of cool/scary, but what is it? And why should you care? Short version? It's the data in your organization that you don’t see, don’t (or can’t) track, and there’s a LOT of it. Dark data lurks in the storage shadows of your organization – filled with overlooked or unknown insights that could lead to potential exposure, cyber threats, compliance risks, and more.
This rapidly expanding reservoir of dark data lives throughout your systems and data repositories – obscure logs, metadata trails, encrypted databases, emailed attachments, abandoned projects, and legacy archives. Like exploring a cavern with a dim flashlight, you get the sense there’s something worthy of further exploration, but you can’t quite define the scope because you lack the tools to give you a clear picture.
Yet this obscure data can, and already is, putting your organization at avoidable risk. Analysts estimate over 80% of an organization's data qualifies as dark. What trends, threats, and patterns are hidden out of sight? What approach can reveal and remediate potential risks associated with these overlooked data stores?
Next-gen Security Analytics solutions can provide the visibility needed to chart this unmapped territory. AI-driven analysis is particularly adept at uncovering subtle patterns in massive data sets that can reveal e.g. hidden APTs (advanced persistent threats), system intrusions, regulatory non-compliance, lapses in data governance, and potential emerging business risks.
The digital innovation that drives most businesses has, ironically, also produced an explosion of undiscovered dark data. Your organization’s next defensive breakthrough very likely resides in these unaudited information resources, but you need the right searchlights to uncover unidentified exposures. Powerful AI security analytics tools are ready to uncover this data, refine it into intelligence, and illuminate an actionable path forward.
To make this workable, let’s look at specific examples within dark data as it applies to cybersecurity. Some of the potential top opportunities to leverage "dark data" include:
- Analyzing log data – Massive and unending volumes of log data from networks, endpoints, SaaS apps, etc. often go uninspected due to being unstructured and overwhelming. Having the right tools to analyze this vast repository is an excellent way to uncover hidden potential threats. It would also be convenient to be able to process petabytes of data in seconds, right?
- User behavior analytics – Details on user activities, anomalous behaviors, and insider threats can be extracted by aggregating identity and access data across systems. Since most risks are introduced by users, correlating this information quickly can significantly improve your security posture.
- Passive DNS analysis – Collecting and linking DNS requests can uncover malicious domains used for command and control or data exfiltration.
- Data loss prevention – Dark data repositories like file shares, databases, and cloud storage can be analyzed to find risky data exposure and misuse.
- End-of-life system data – Asset management data can reveal vulnerabilities for EOL systems no longer getting patches/support.
- Appending public data – Combining organization data with public breach corpora, (is corpora a word?) WHOIS domain data, threat feeds, etc. can provide external context to detect threats.
- Uncovering toxic data – Scanning stored datasets to ensure they don't include private, toxic, or weaponized data that could cause brand, ethics, or data poisoning issues if deployed.
Getting visibility into these vast reservoirs of dark data can expose risks and threats that evade existing security measures. This problem already exists in your organization, it's growing by leaps and bounds, and this trend is accelerating asymptotically. You can’t kick this can down the road, so the sooner you address this issue the better off everyone in your organization (and your customers) will be.
Introduction
Security teams adopted the Security Information and Event Management (SIEM) as the central hub for all things security - including collection, correlation, and analysis of log data and alerts for security and compliance purposes. The problem, as is the case with any major technology, is that traditional SIEMs were not built to be the one-stop shop for modern security challenges. We work with security teams every day grappling with the increasing demands for logging performance and scalability in today's dynamic threat landscape, not to mention the ability to integrate with ever-changing security tools.
As tools change, and adversaries operate at an unprecedented pace, organizations must prioritize capabilities that facilitate rapid threat identification and response across the organization - and they have to do this in a way that doesn’t disrupt the investments they’ve made, in both people and technology.
We've had the same mission from day 1: Finding malicious actors within your environment using the world's largest and best repository of "known bad" activity patterns and intelligence. The technology landscape has changed with cloud adoption and fragmented data sets, making it siloed, voluminous, expensive, and specialized to interact with. To continue our mission, we are aggregating and bringing all of your data in one place at a very reasonable price point.
Legacy SIEMs: High Costs, High Complexity
Search timeouts, scalability issues, and limited CTI utilization leave legacy platforms built on data architecture with a lot to be desired when it comes to core security functions like threat detection and incident response. Not to mention, most legacy platforms require copious modules and disparate systems to achieve optimal functionality.
Index-based searching highlights challenges as log volumes and the number of log sources increase. Growing indexes can impede search speed, making it challenging to identify and thwart threats effectively.
On top of it all, legacy SIEMs come with exorbitant costs - and for good reason, as many were not built as a cloud-first platform in today’s landscape. The expense associated with logging everything often forces organizations to selectively log data, leading to blind spots and missed attacks. Moving data to Anomali - especially the high-value security data, like endpoint, firewall, and network traffic, offers a cost-effective solution, potentially saving up to 75% compared to legacy SIEMs and their non-cloud native storage capabilities.
Adding a modern platform to address core SIEM use cases
Legacy SIEMs can provide tremendous value, but oftentimes with the aforementioned challenges attached. Embracing a hybrid model with Anomali delivers outstanding performance and low latency, reducing incident response times and fortifying overall security.
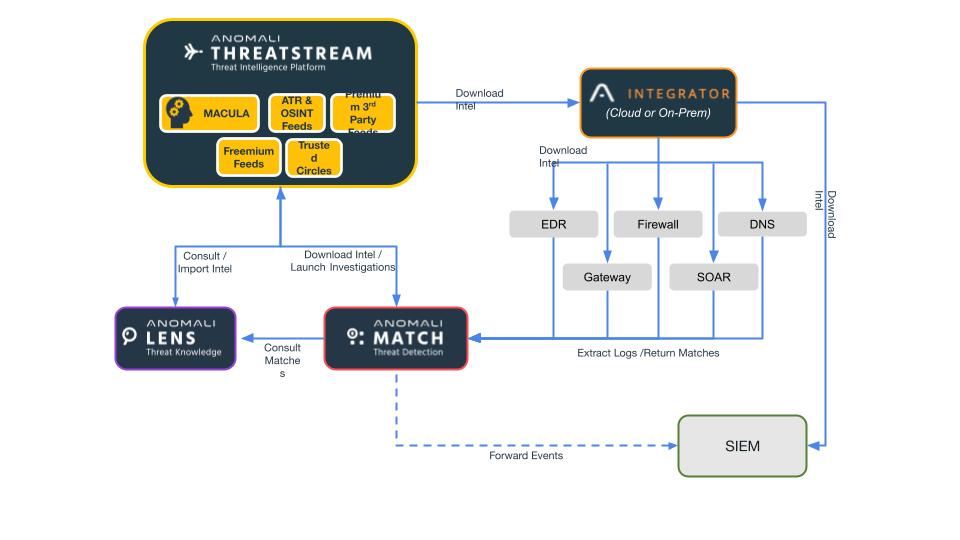
Anomali: Ideal for Today's Toughest SIEM Use Cases
The Anomali Platform, evolving from the industry-leading Threat Intelligence Platform, emerges as a contemporary log management platform that excels in storing, analyzing, and swiftly accessing data at scale. Its rapid search capabilities, real-time alerting, CTI database, and customizable dashboards make it optimal for various security use cases.
Key SIEM Use Cases that Anomali Can Solve
Threat Hunting with all available Threat Intelligence
Anomali Log Management provides the speed, scale, and querying flexibility essential for proactive threat hunting. Its query language supports Natural Language Search (available in a variety of languages), empowering security teams to optimize searches and swiftly pinpoint threats. Integration with the largest repository of Indicators of Compromise (IOCs) adds valuable context to threat hunts.
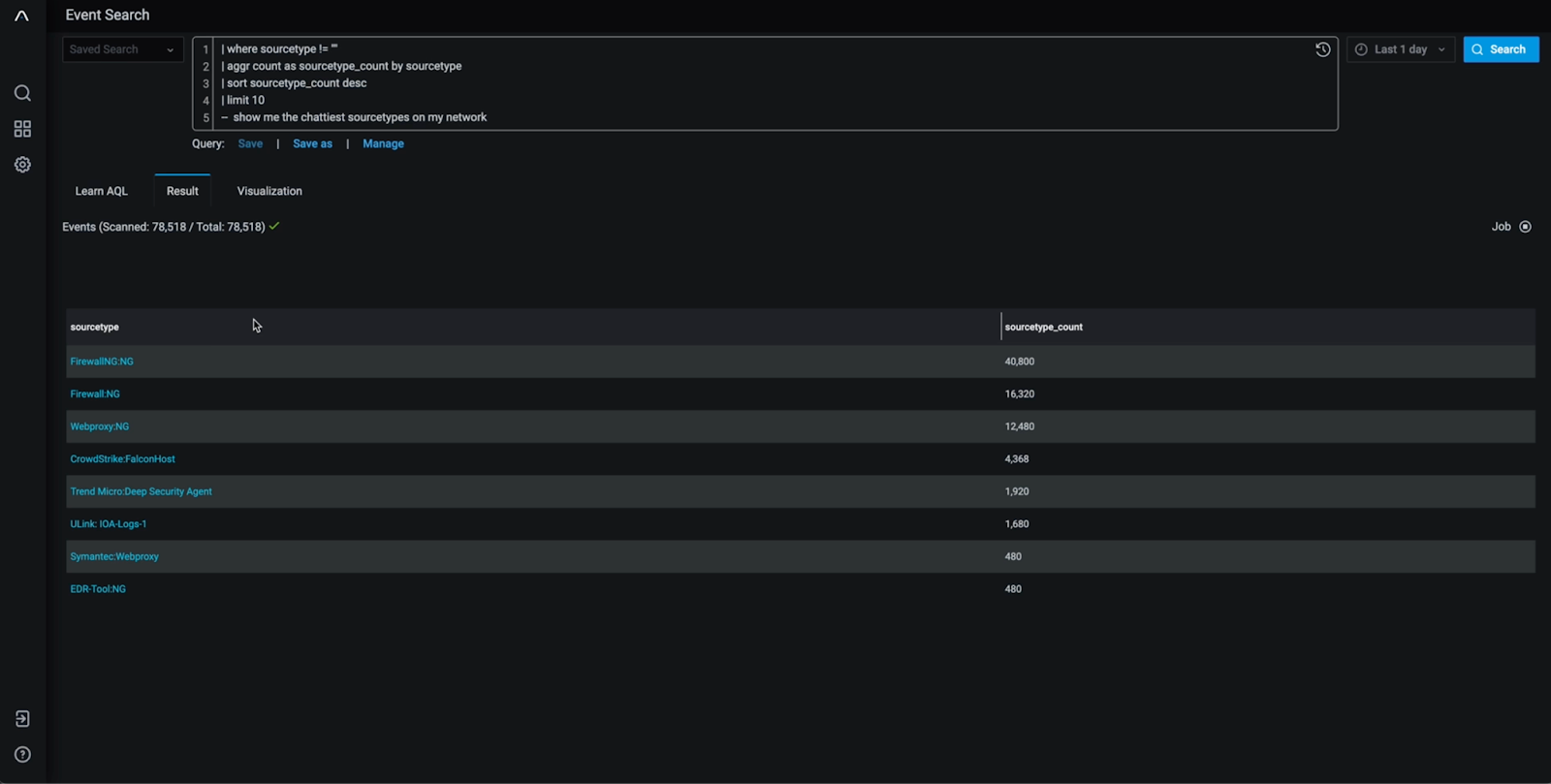

Incident Response and Forensics
In incident response scenarios, time is of the essence. Anomali Log Management facilitates effective incident response and forensics by offering cost-effective, long-term data retention. Its scalability allows organizations to log even the chattiest datasets, taking heavy lifting off of the SIEM while providing a comprehensive dataset for investigating attacks, determining root causes, and reconstructing events. Findings from a recent stress test of the Anomali Platform showed that users could query over a petabyte of data and receive results in 3-4 minutes.
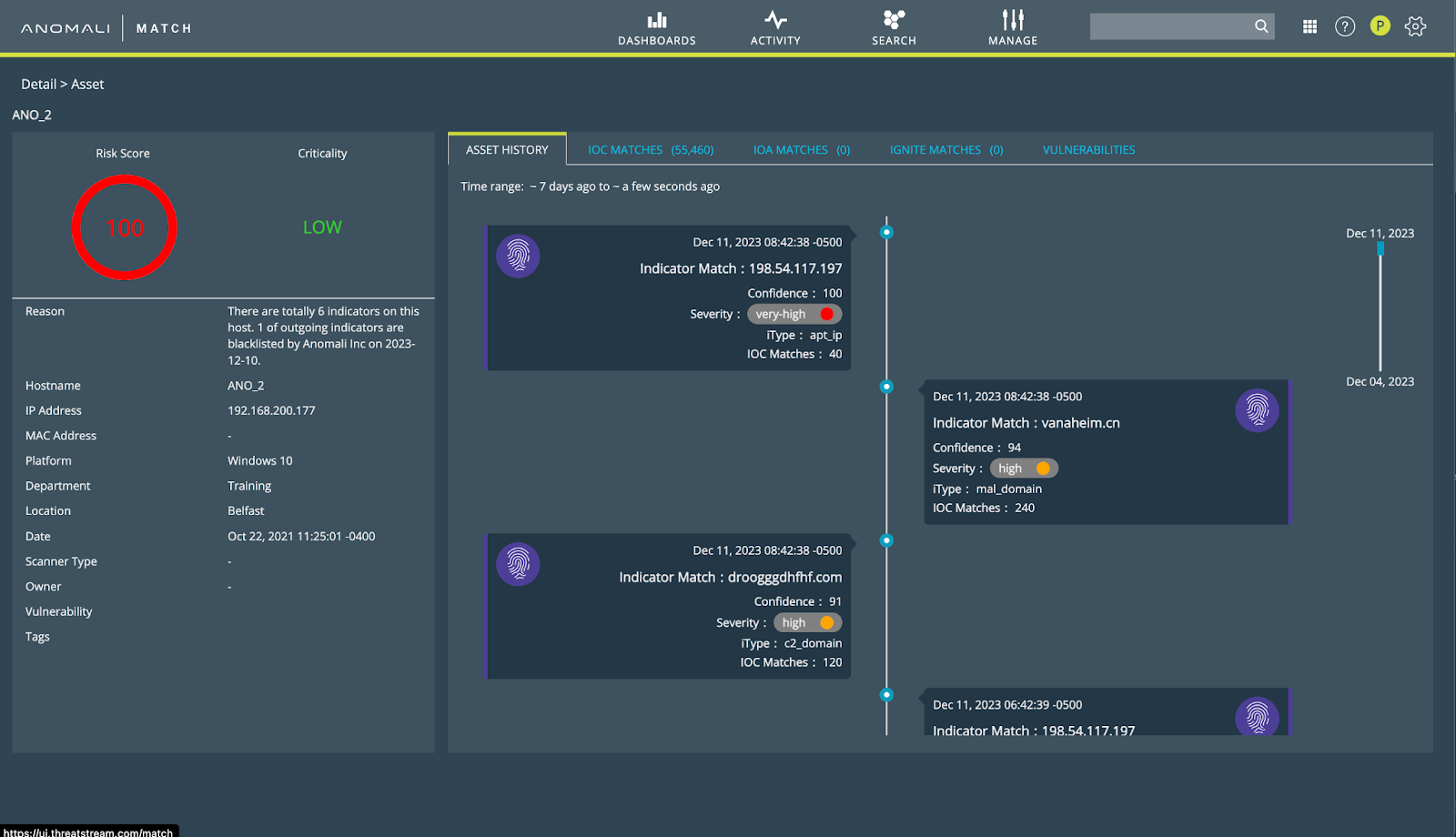
Data Retention and Backup
Anomali addresses compliance challenges by providing scalable, affordable long-term data storage. Organizations can meet evolving compliance requirements - implementing Anomali eliminates on-premise upkeep and costs, high costs of SIEM logging, and provides backup capabilities to ensure swift disaster recovery. Anomali Link supports easy collection and processing of regulated data from various sources, ensuring compliance without escalating costs, or compromising on data availability.
Workforce Utilization and Training
Built on the Anomali Query Language - users of the Anomali platform no longer need to rely on complex search queries and certifications. This means Tier One analysts can utilize Natural Language to ask questions like “Show me all hosts that have been affected by Killnet” and get results back within seconds. This also reduces the need for third-party engineering services that quickly inflate costs.
Dashboarding and Alerting - Data Visualization
Anomali offers real-time visibility into security status, enabling organizations to analyze trends, detect threats, and troubleshoot issues. Its streaming engine updates searches and dashboards upon data arrival, allowing instant anomaly detection. Customizable dashboards and pre-built options, as well as additional applications from the Anomali App Store enhance visualization and information sharing.
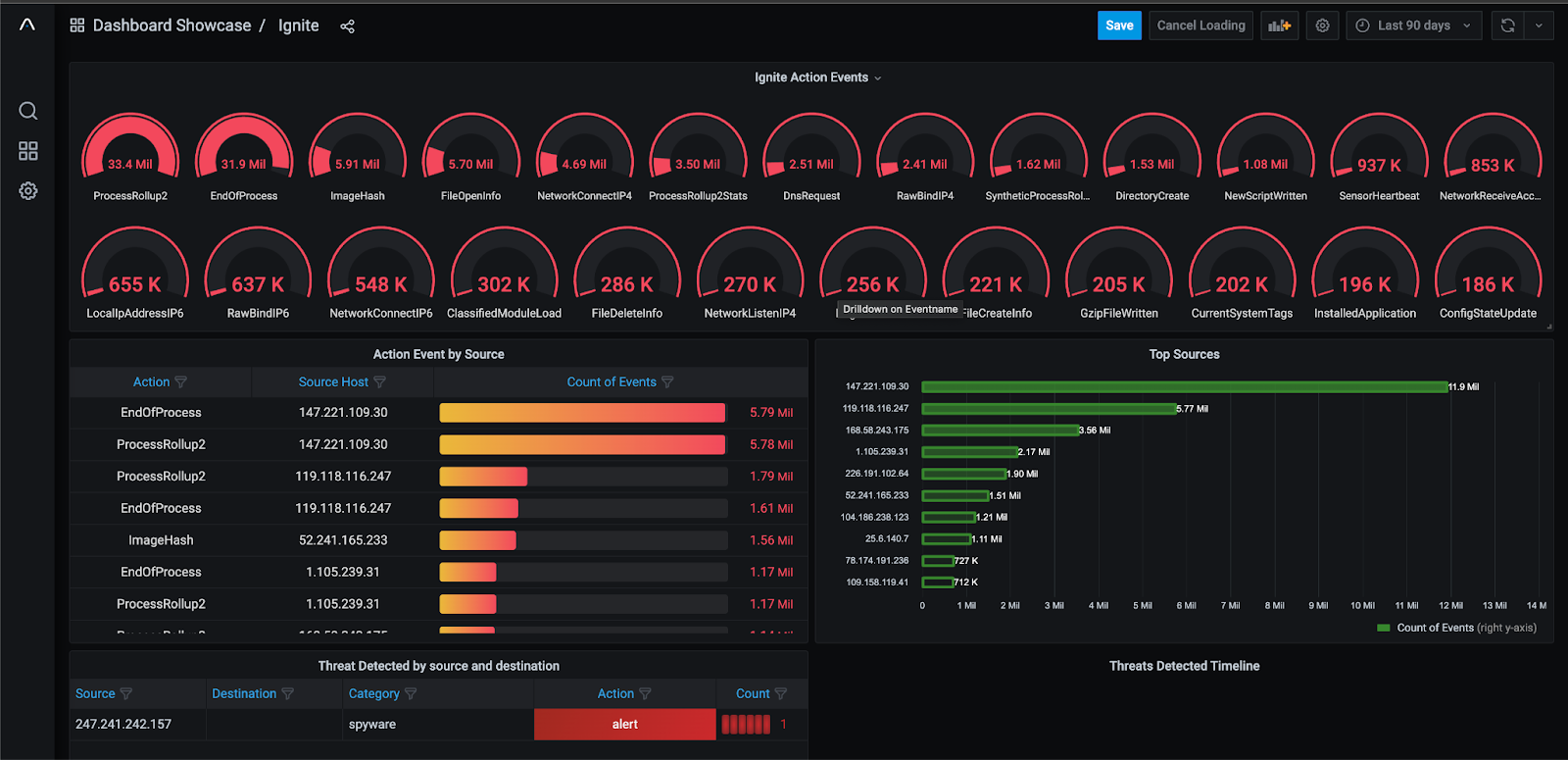
Conclusion
Through working with our customers and partners, we’ve found that security teams are looking for a better way to hunt and search their data, and leadership teams are looking to save dollars wherever they can. Anomali stands as a powerful and versatile tool for organizations seeking optimal speed, scale, and total cost of ownership to address their toughest SIEM use cases. We aim to enhance your security team’s performance with cloud-native search, and storage scalability, all while providing better economic outcomes.
Given the genuine sense of urgency that drives most cybersecurity initiatives, the ability to swiftly and accurately query log files is critical. Log files are a record of anything that has happened within a computer, application, or network, including event information, timestamps, categorization schemas, and so on. As a forensic tool, it can provide tremendous amounts of details needed to identify existing and potential risks.
Traditional methods of querying log files often involve complex Structured Query Language (SQL) queries, posing challenges for Security Operations Center (SOC) analysts. This blog explores the transformative advantages of using natural language for log file queries. From liberating analysts from SQL complexities to enhancing Indicator of Compromise (IOC) detection, seamlessly correlating with Threat Intelligence Platforms (TIPs), and enabling the capability for extensive lookbacks, natural language processing emerges as a game-changer in the arsenal of cybersecurity professionals.
The Burden of SQL and Liberation through Natural Language Processing
Traditional log file queries, predominantly executed through SQL, have long been a staple in cybersecurity. However, the intricacies of SQL can act as a double-edged sword. While it provides a powerful means to extract specific information from databases, its complexity can hinder the efficiency of SOC analysts. Natural language processing, with its intuitive and human-readable syntax, allows analysts to query log files without the need to master SQL intricacies.
Advantage #1: Simplifying Query Complexity
Natural language queries free SOC analysts from the shackles of SQL intricacies. Analysts can articulate queries using everyday language, significantly reducing the learning curve and enabling faster, more efficient log analysis. This simplicity contributes to a more agile and responsive cybersecurity environment. Here is an example:


That’s it. And let’s face it, if you’re an analyst under pressure, which would you rather write, assuming the same end result?
Additionally, when implemented properly, the original query language is still displayed next to the natural language query, just in case someone wants to get their hands in the innards of a query.
Advantage #2: Enhanced Analyst Productivity
By removing the need for SQL expertise, natural language queries empower SOC analysts (particularly T1 analysts) to focus on what matters most—identifying and responding to security threats. Analysts can now allocate their time and energy to more strategic tasks, enhancing overall productivity and responsiveness to emerging threats.
Improved IOC Detection and Remediation
The agility provided by natural language queries transcends mere convenience; it directly impacts the efficacy of detecting and remediating Indicators of Compromise (IOCs). The intuitive nature of natural language allows for more nuanced and precise queries, facilitating the swift identification of suspicious patterns and behaviors.
Advantage #3: Precision in IOC Identification
Natural language queries enable analysts to craft highly specific queries tailored to the unique characteristics of IOCs. Analysts can articulate queries that cut through the noise, honing in on potential threats with unparalleled precision, whether it's a specific IP address, file hash, or behavioral pattern.
Advantage #4: Rapid Remediation Actions
The immediacy of natural language queries translates into swift remediation actions. Analysts can promptly identify compromised assets, initiate containment measures, and mitigate the impact of security incidents. This agility is crucial in minimizing the dwell time of threats within the network.
Seamless Correlation with TIP Data Sources
A holistic cybersecurity strategy demands seamless integration and correlation with Threat Intelligence Platforms (TIPs). Natural language queries facilitate this integration, enabling SOC analysts to cross-reference log data with external threat intelligence feeds effortlessly.
Advantage #5: Real-time Threat Intelligence Integration
Natural language queries pave the way for real-time correlation with external threat intelligence sources. Analysts can dynamically incorporate the latest threat intelligence into their queries, staying ahead of evolving threats and enriching their analyses with up-to-the-minute context.
Advantage #6: Contextual Analysis for Informed Decision-making
By effortlessly integrating external threat intelligence, natural language queries empower SOC analysts to conduct contextual analyses. This contextual understanding enhances the decision-making process, ensuring that responses to security incidents are informed, strategic, and aligned with the broader threat landscape.
Extensive Lookbacks: Years, Not Just Months
One of the transformative advantages of natural language queries in conjunction with a cyber data lake in log file analysis is the ability to conduct extensive lookbacks through petabytes of data, often in seconds. Unlike traditional methods that often limit lookbacks to a few months, natural language queries combined with cyber data lake storage opens the door to immediate retrospective analysis spanning years.
Advantage #7: Historical Context for Long-term Analysis
Natural language queries, backed by efficient indexing and search capabilities, facilitate extensive lookbacks into historical log data. This historical context is invaluable for uncovering long-term threat trends, identifying persistent threats, and conducting comprehensive post-incident analyses.
Advantage #8: Compliance and Forensic Investigations
The capability for years-long lookbacks is advantageous for cybersecurity analytics and crucial for compliance requirements and forensic investigations. Natural language queries enable organizations to meet regulatory obligations by providing a comprehensive historical record of security events.
Embracing the Future of Log File Queries with Natural Language Processing
Cybersecurity constantly evolves, and natural language queries are emerging as a revolutionary tool for improving efficiency and accuracy. Using natural language processing simplifies the complexity of queries, allowing SOC analysts to detect better and remediate IOC, correlate with TIP data sources, and conduct extensive lookbacks over extended periods, making it a game-changer for how analysts interact with log files. Embracing the intuitive power of natural language is not merely a choice but a strategic imperative for those seeking to stay ahead in the relentless pursuit of cyber resilience.